Introduction
Keeping your data secure is critically important. Aspera strongly
encourages you to take additional steps in setting up and configuring your
SSH server so that it is protected against common attacks. Most automated robots
will try to log into your SSH server on Port 22 as Administrator,
with various brute force and dictionary combinations in order to gain access to your
data. Furthermore, automated robots can put enormous loads on your server as they
perform thousands of retries to break into your system. This topic addresses steps
to take in securing your SSH server against potential threats, including changing
the default port for SSH connections from TCP/22 to TCP/33001.
Why Change to TCP/33001?
It is well known that SSH servers listen for incoming connections on TCP Port 22. As
such, Port 22 is subject to countless, unauthorized login attempts by hackers who
are attempting to access unsecured servers. A highly effective deterrent is to
simply turn off Port 22 and run the service on a seemingly random port above 1024
(and up to 65535). To standardize the port for use in Aspera transfers, we recommend
using TCP/33001.
Please note that your Aspera transfer product
ships with OpenSSH listening on both TCP/22 and TCP/33001. As such, Aspera
recommends only exposing TCP/33001 through your organization's firewall and
disabling TCP/22.
NOTE: Remote Aspera application connections attempt to
establish an SSH connection using the default port 33001. However, if the connection
fails, the application attempts the connection using port 22.
The following explains how to change the SSH port to 33001 and take additional steps
for securing your SSH server. The steps all require Administrator
access privileges.
-
Locate and open your system's SSH
configuration file
Open your SSH configuration file with a text editor. You will find this
file in the following system location:
| OS Version |
Path |
| 32-bit Windows |
C:\Program Files\Aspera\Enterprise Server\etc\sshd_config |
| 64-bit Windows |
C:\Program Files (x86)\Aspera\Enterprise
Server\etc\sshd_config |
-
Add new SSH port
Note: Before changing the default port for SSH connections, please verify with your
network administrators that TCP/33001 is open.
The OpenSSH suite included in the installer uses TCP/22
and TCP/33001 as the default ports for SSH connections. Aspera recommends
disabling TCP/22 to prevent security breaches of your SSH server.
Note: When changing the SSH port, you must also update the SshPort
value in the <WEB...> section of
aspera.conf. Please refer to Configuring your Web UI
Settings for details.
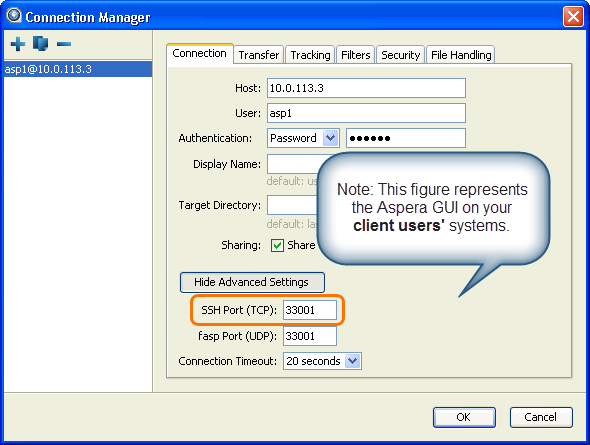
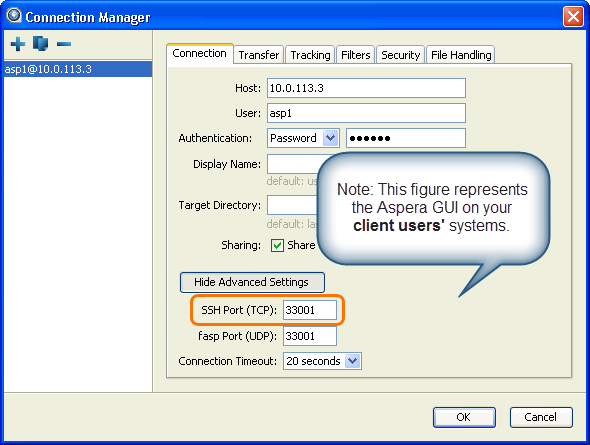
Once your client users have been
notified of the port change (from TCP/22 to TCP/33001), you can disable Port
22 in your sshd_config file. To disable TCP/22 and use only
TCP/33001, comment-out Port 22 in your sshd_config
file.
...
#Port 22
Port 33001
...
Note: Aspera recognizes that disabling the default SSH connection port (TCP/22) may
affect your client users. When you change the port, ensure that you
advise your users on configuring the new port number. Basic instructions
for specifying the SSH port for fasp file transfers can be found
below. To change the SSH port for Aspera Client, click
Connections on the main window, and select
the entry for your computer. Under the Connection
tab, click Show Advanced Settings and enter the
SSH port number in the SSH Port (TCP) field.
To make an impromptu connection to TCP/33001 during an
ascp session, specify the SSH port (33001) with the -P
(capital P) flag. Please note that this command does not alter ascp or
your SSH server's configuration.
-
Disable non-admin SSH tunneling
Note: The instructions below assume that OpenSSH 4.4 or newer is installed on your
system. For OpenSSH 4.4 and newer versions, the "Match" directive allows
some configuration options to be selectively overridden if specific
criteria (based on user, group, hostname and/or address) are met. If you
are running an OpenSSH version older than 4.4, the "Match" directive
will not be available and Aspera recommends updating to the latest
version.
In OpenSSH versions 4.4 and newer, disable SSH tunneling to avoid potential attacks; thereby
only allowing tunneling from Administrator group users. To disable non-admin SSH
tunneling, open your SSH Server configuration file, sshd_config, with
a text editor.
Add the following lines to the end of the file (or modify them if they already exist):
...
AllowTcpForwarding no
Match Group Administrators
AllowTcpForwarding yes
Depending on your sshd_config file, you may have additional instances of
AllowTCPForwarding that are set to the default
Yes. Please review your sshd_config
file for other instances and disable as appropriate.
-
Update authentication methods
Public key authentication can prevent brute force SSH attacks if all password-based
authentication methods are disabled. For this reason, Aspera recommends
disabling password authentication in the sshd_config file
and enabling private/public key authentication. To do so, add or uncomment
PubkeyAuthentication yes and comment out
PasswordAuthentication yes.
...
PubkeyAuthentication yes
#PasswordAuthentication yes
PasswordAuthentication no
...
Note: If you choose leave password authentication enabled, be sure
PermitEmptyPasswords is set to
"no".
PermitEmptyPasswords no
-
Restart the SSH server to apply new settings
When you have finished updating your SSH server configuration,
you must restart the server to apply your new settings. Restarting your
SSH server will not impact currently connected users. To restart
your SSH Server, go to . Locate the OpenSSH Service and click
Restart.
-
Restrict user access
Restricting user access is a critical component
of securing your server. When a user's docroot is empty (i.e. blank), that
user has full access to your server's directories and files. To restrict the
user, you must set a non-empty docroot, which automatically changes the
user's shell to aspshell (Aspera shell). You can do so from
the product GUI by going to . Input a path in the blank field and ensure that
Override is checked.
Once you have set the user's docroot, you can further
restrict access by disabling read, write and/or browse. You may do so via
the product GUI (as shown in the screenshot above).
| Field |
Description |
Values |
| Absolute Path |
The area of the file system (i.e. path) that is accessible to
the Aspera user. The default empty value gives a user access to the
entire file system. |
Path or blank |
| Read Allowed |
Setting this to true allows users to transfer
from the designated area of the file system as specified by the
Absolute Path value. |
|
| Write Allowed |
Setting this to true allows users to transfer
to the designated area of the file system as specified by the
Absolute Path value. |
|
| Browse Allowed |
Setting this to true allows users to browse
the directory. |
|
-
Review your logs periodically for attacks
Aspera recommends reviewing your SSH log periodically for
signs of a potential attack. Launch . To see only SSH Server events, select to bring up the filter settings. In tab, select sshd in the
Event source menu to display only SSH Server
events. You may also apply other conditions when needed.
With a filter applied, you can review the logs in the Event
Viewer main window, or select to export a log file using .txt or
.csv format.
Look for invalid users in the log, especially a series of login attempts with
common user names from the same address, usually in alphabetical order. For
example:
...
Mar 10 18:48:02 sku sshd[1496]: Failed password for invalid user alex from 1.2.3.4 port 1585 ssh2
...
Mar 14 23:25:52 sku sshd[1496]: Failed password for invalid user alice from 1.2.3.4 port 1585 ssh2
...
If you have identified attacks:
- Double-check the SSH security settings in this topic.
- Report attacker to your ISP's abuse email (e.g.
abuse@your-isp).
-
Set up transfer server authentication
For transfers mediated by a web application, the client browser sets up the
context for the transfer using an HTTPS connection to the server, and then
delegates the transfer to the Aspera fasp engine. The fasp
engine then connects to the transfer server. In so doing, it needs to ensure
the server's authenticity in order to protect the client against server
impersonation and man-in-the-middle (MITM) attacks.
To verify the authenticity of the transfer server, the web app passes the
client a trusted SSH host key fingerprint of the transfer server.
When connecting to the transfer server, the client confirms the server's
authenticity by comparing the server's fingerprint with the trusted
fingerprint.
Draft comment: Jim
Note to self: See ssh-server_NOTES.txt for previous
versions of the above wording.
To configure transfer server authentication, open the transfer server's
aspera.conf file:
C:\Program Files[ (x86)]\Aspera\Enterprise Server\etc\aspera.conf
Locate the <server> section, and add the
<ssh_host_key_fingerprint> option.
- <ssh_host_key_fingerprint>
<ssh_host_key_fingerprint>fingerprint</ssh_host_key_fingerprint>
To
retrieve the SSH fingerprint, locate the transfers server's public
or private key, and run the following command on a Linux, Mac, or
other UNIX
computer:
# cd /etc/ssh
# cat ssh_host_rsa_key.pub | cut -d' ' -f2 | base64 -d | sha1sum | cut -d' ' -f1
The
following is an example SSH
fingerprint:
43:51:43:a1:b5:fc:8b:b7:0a:3a:a9:b1:0f:66:73:a8
By
convention, Aspera uses a hex string without the colons ( :
). For
example:
435143a1b5fc8bb70a3aa9b10f6673a8
The
aspera.conf setting for this key would then be as
follows:
<ssh_host_key_fingerprint>435143a1b5fc8bb70a3aa9b10f6673a8
</ssh_host_key_fingerprint>
After modifying aspera.conf, be sure to restart the node service by
running asperanoded:
> sc stop asperanoded
> sc start asperanoded